A real hacker, not calm inside.
If you see Yuan Ge, almost doubt that judgment. You can't put this kind even Harper's uncle and that year relied on a piece of code can freely access all personal computers and servers "God of cyberspace" link.
But trust me, once in his spiritual world, you'll see the waves.
Compared to writing and language, Yuan Ge more accustomed to using digital lyric and code. A silent man constantly asked the world for answers, repeatedly overturned people's fundamental understanding of cyberspace.
Reality is so scary, we love this story.

"Yuangeyuanrenguang"
A pen, a book, a game
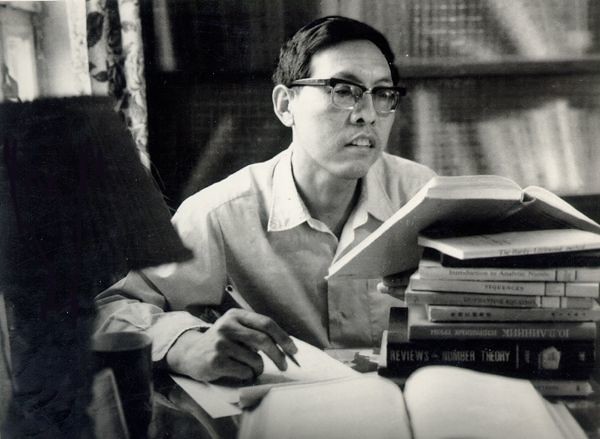
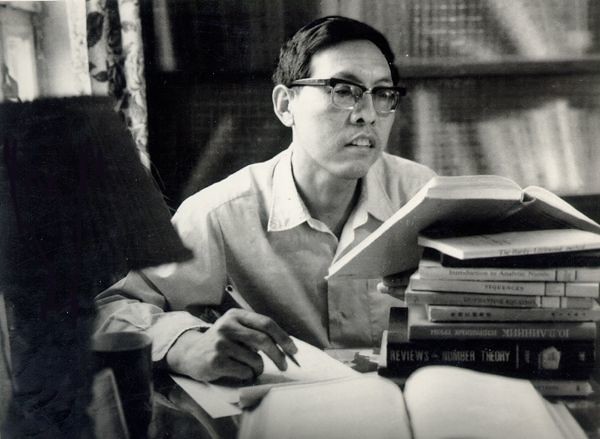
Those enamored of mathematics, who has a calm atmosphere. When Yuan Ge, Yuan Ge and small time, precisely when in elementary school, already holds mathematics books a day, standing in the roaring days.
I was born in the countryside, home conditions were not good, so I had in primary school library or the Xinhua Bookstore in the town to see my favorite book. Fortunately my interest mathematics books, sales are not too good. Cents, two cents can buy a book. But even so, I find it difficult to afford, only one favorite, the thickest and most expensive one home.
When it comes to school, Yuan Ge has started to look at graduate student group on the content of the Boolean algebra of the symmetry identities, you can head up the students eyes when he is holding the book.
Buy these books are paid for.
When it was junior high school, a ballpoint pen is nice stationery. Once I and home to a few cents I want to buy a ballpoint pen. But I did well in the exam, get school award is a ball pen. I told them this is what I bought and saved money to buy a book.
This incident, my brother "informer", Yuan Ge end was beaten by his father. That time, poverty walk in front of the material poverty of the spirit. Yuan Ge is beating a book obviously lucky it's not too bad.
Math and logic of paranoia, allowing him to get along with a unique perspective and the world.
I have a classmate's older brother, likes to play chess, so I'm interested in chess endgame. Next pieces there is an important principle, that is not in accordance with the thinking of most people, but to consider all the logical possibilities. In normal times, you won't get the car for others, but in pieces, you have to consider the space, in fact, every step a step can be abstracted into a Boolean algebra, logical, mathematical methods can solve the puzzle.
In addition to master is the mess outside, juvenile Yuan Ge is poker puzzle master, master brain teasers. Maybe for him, nothing is more sexy than the strict logical thing in the world. Dolce & Gabbana iPhone 6 Case
"When he was President of Shandong University, Pan Chengdong, a mathematician"
Windtalker
Admire, President of Shandong University, mathematical master of Pan Chengdong fame seriously leaning branch Yuan Ge rely on mathematics and physics two almost perfect grades narrowly entered the Department of mathematics of Shandong University. However, Yuan Ge faces a thorny issue at the University, that is almost all of the courses he completed the study in high school. Sit in class in a daze is a kind of torture for him to sleep.
"I don't want to go to classes, I prefer to learn, because learning to learn faster, deeper. "His argument is simple and straightforward. Yuan Ge on the hunt for a new world that fascinated him, the computer walks into his life.
1993-1997 is Yuan Ge College cyber world did not like this into the vastness of the ocean. Computer viruses are often spread through floppy disks from one computer to another computer. Yuan Ge recalls that just want to "understand viruses this piece." Once Yuan Ge to figure out something, that is true, clear, white. You know.
Due to the special properties of the virus, they tend to spread via computer the underlying logic. "Follow" virus Yuan Ge, also came to the bottom of the cyberspace. The Assembly language of the computers work, the principles of operating systems principles of disk controllers, Yuan Ge on a lesson not to spend all day reading these books in the library.
Machine is on the money in school, so I can't stay in the room. I use debug disassembly room operating system BIOS code encounter code that requires careful study, I use the school exercise-books copied down. Some code is translated into high few lines of code, but because my copy is to the underlying Assembly code, is very large. Then I found out that homework is my copy was full.
For him, the University for four years, the most powerful skills, ability to communicate is the master of the soul and computers--binary language. Computer, binary code like everyone used to think of "accent", there is no language could be more than binary "machine heart". Yuan Ge now when looking at the binary code, and can automatically fill out the brain of high-level language source code, people like this thinking in computer world, not many around the world. He was like a "wind speaker", a lyric in the eyes of ordinary people like the wind.
The underlying principle of the computer is boring, but if you are interested in it, you find that this principle can understand and control a computer's basic functions, it is very comfortable. If your computer is good, add some input, basic can be Daniel.
Yuan Ge says.
Yuan Ge College not only overripe in mind a variety of programming languages, from the virus was seen on the most treacherous sophisticated use of language. Yuan Ge recalls:
For example, the famous ghost virus can automatically deformation, which breaks the rules relies on Avira virus signatures;
For example DIR virus can completely bypass the antivirus mechanisms, created a new way of infection.
"Pirate dealers" I
Yuan Ge, out of all imprisoned in this cyber world, is his immortal River. In addition to break beyond the school room antivirus card causes the virus raging, cracking its fried-day anti-virus software "KV300" is also one of his actions.

"At the end of one of the most popular antivirus software (no): KV 300 antivirus floppy"
At that time I was working on a CPU to run special mechanisms: DMA. Some information is transmitted directly by the CPU, you might want to wait for a long time, so you can achieve auxiliary transmission controlled directly by the DMA controller memory, CPU share some of the work. I found that this mechanism can be used, because every time after a DMA transfer is completed, will generate an interrupt, if blocking at this time, it can resolve its operations on the disk. In this way the cycle, you can read entire anti-virus information of a floppy disk, completely bypassing its encryption technology.
When other people do crack, from time to time be jiangmin blocked, but I cracked disk, whenever you update the virus definitions, it can be used normally.
For the year of "works", Yuan Ge is very satisfactory. So much so that when he didn't pass the English four levels and not get diplomas and degree certificates, he even thought of, if you can't find a job, to sell the pirated disc. "They sell genuine 260, 360, I just one-tenth price, 26, 36, should be in business. "
Yuan become, God does not give "pirate dealers" opportunity, he is also in the Hisense landed the position of a single-chip development.
An instant success
People familiar with another hacker Torchbearer Zhang Xun Dee knows, because hotel first served access to broadband, he was on the road to security research, founded the hacker community, Huangpu Military Academy "security focus." Similar to di and Zhang Xun, Yuan Ge access to the Internet, because 1997 Hisense applied for a network line, which allows the Yuan Ge to work on new issues. This time, he wanted to make a network protocol. You should know, according to Yuan Ge script, as long as he "engaged in", it must have been to get crispy on outside again.
When I was studying network protocol, while reading memory, disassembled into the binary code of the control. It's like learn English memorizing words and dialog to remember.
Because no test had never graduated from CET hackers actually has a sense of humor in English, for example.
Real world there are countless kinds of logic, and each logical, as long as it exists, how bizarre, how hard to imagine that weapons may have been changing the world. Yuan Ge caught a look weird logic door.
Windows 9X, the popular network shared documents. When I study the Commons code found, the server authenticates the client when password authentication, password length check is based on information from clients shall prevail. This thing looks really weird. Because experience tells us that the length of the password, the password must be stored on the server. I'll write the validation code from the information sent by the client, tells the server to validate only one byte, the server was only one byte. One byte only 256 possible, very good crack.
Yuan Gehei into the computers of co-workers and managers, watching their wages, while lamenting the world's magic and aspired to be a cyber security expert.

"Windows 98 interface (for your nostalgia)"
It was his discovery of the first real sense of vulnerability. Since then, the Yuan Geyi hand.
Vulnerability he discovered the famous Windows share password authentication, you can freely access shared files;
He was involved in creating the domestic established security company NSFOCUS, developed many high risk vulnerability IIS server, you can freely access any IIS Web servers;
He studies each PC using RPC protocols, RPC service buffer vulnerability found many serious, you can break the permissions on all Windows computers, and remote intrusions.
The beginning of 21st century, the rapid spread of the Internet in the tide, many techies login hacker forums, Yuan Ge has become a spiritual beacon of the hacker community.
Initially, Yuan Ge actively submitted to Microsoft vulnerabilities found, but when Microsoft is not willing to pay for the vulnerability of Microsoft, other noncommittal attitude submit let the Yuan gradually lost the passion, that in 2001, when Yuan Ge discovered can be used against any fatal flaws with the RPC service on a computer, he chose to be silent. Until two years after the United States via the same technology to produce 18-year-olds Jeffrey Blaster worm virus that swept halfway around the world.
Data stream--the cyber world of inception
By 2000, Microsoft's attitude towards the white hat is cool, but this does not prevent Yuan Ge exploration of network security. Yuan Ge, this was his life's "high-yield". Eat, sleep, go to the toilet every day of the time code. Core proposition is that he consider--could use a common security model to assist or even replace their own mining hole.
To understand Yuan Ge tool, you need to first understand the nature of vulnerability.
Is the nature of computer programs. Based on the input data, a bunch of code inside your computer opens an infinite number of doors, and ultimately as a result. Information entered when certain special conditions are met, it will be found inside your computer opens a strange door and tried to open it. At this time, the cyber world will face collapse, a vulnerability.
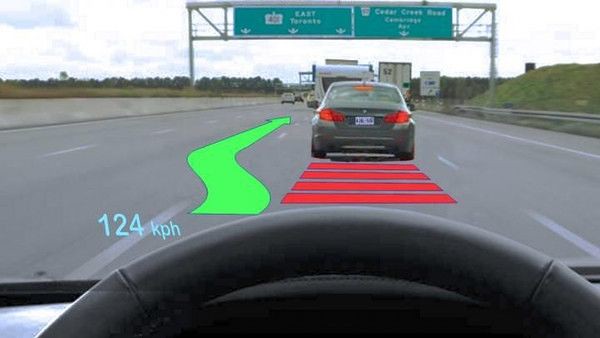
In other words, find the specific code, and you'll find a vulnerability that can defeat the system. Vulnerability mining in two main directions:
1, fuzz testing. Fuzz testing is a kind of black box testing, by random data to the system, observation systems are normal reactions. However, a system which is so large, the information you enter there are countless possible, this vast possibility space is exponential. So if a blind test, even if the universe is destroyed and can't even test all possibilities of one-.
2, white-box testing. By studying the system's source code or binary code, find the logical flaws and potential problems. This approach is equally questionable, it is a complex program, code large has gone beyond the people's ability to read. And there are many painted interface in a program code, this is not a vulnerability mining concern, but before reading, you can't exclude these useless code. Dolce Gabbana iPhone Case
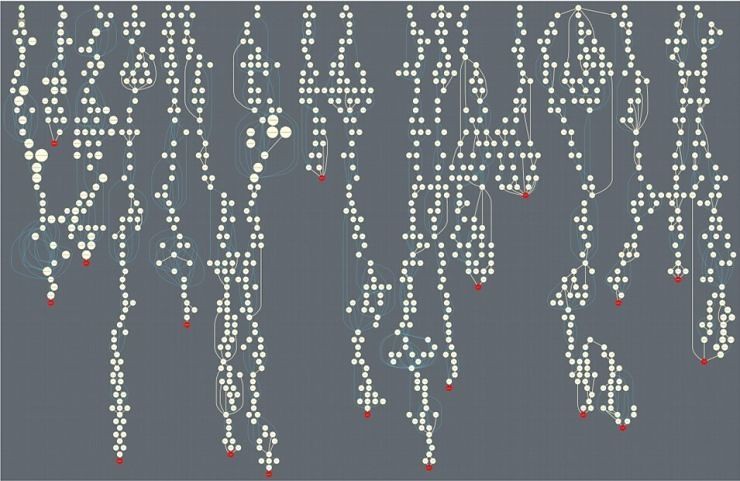
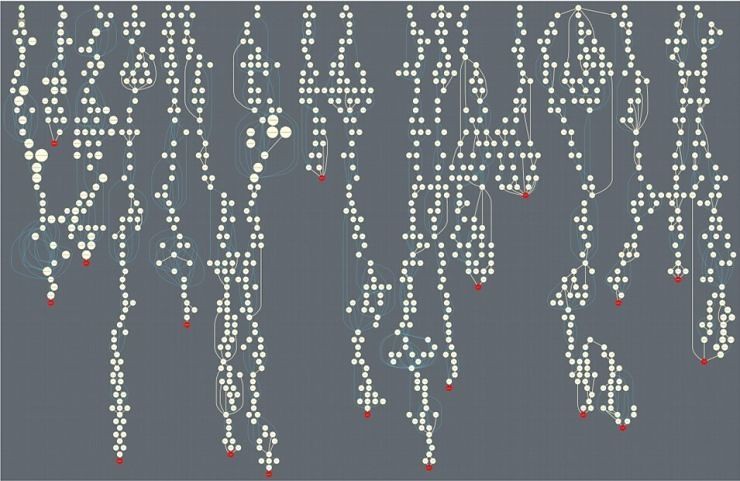
"Run the logic tree diagram software"

Yuan Ge tool with a fuzz testing and white box testing, what he calls "data flow" test method.
Points of interest according to the researcher, constructing targeted data and let the system handle it. In the course of processing, you can use breakpoints in the debugger to see the program running in the State, and stay through the debugger code can be reverse-guess what code is this piece of data. In this way, without a lot of code auditing, you can navigate directly to a key piece of code, the disassembly of this code, you can read the "mind". According to this code, presumably all of its logical branching and targeted according to the total amount of these branches to construct a new data, further targeted attempts.
Sounds easy, but this system the hardest is yet to come.
You can read this code, but you need to use mathematical methods of abstracting the contents of this code, all logic to deduce the branches, some humans are very easy to understand logic, wants solved by process automation will require very complex logic description. And a fine for each logical point that might follow the path of many levels, in this case also there are numerous possibilities exist, this relates to constraint solving math problems.
Yuan Ge said.
As shown in the inception, the Yuan Ge for the world of digital and logical insights, deepest Limbo in the cyber world, where there are only a few bytes of maneuver, gave him insight into the truth of the judgment.

The hand of God
Around 2008, tough to resist the invasion of numerous vulnerabilities, exploit mitigation measures be implemented gradually. Such mechanisms will not reduce vulnerabilities appear, but vulnerability has become very difficult. They are like a brick wall, you know vulnerabilities on the other side, but you cannot close. Including DEP, ASLR, emet, including the CFI was effectively launched the exploit mitigation measures.
Yuan Ge stood behind the wall, ready to "go in". Suddenly, he felt the scene before, like nearly a decade ago, a memory.
Back in 1997, the macro virus is spreading, and this is a virus that use scripting code to sabotage. Due to a virus attack can only rely on the script text property, so many research institutions including Jinshan, the destructive power of this type of virus is very limited, even saying it "can only be used to prank".
But Yuan Ge does not think so, he believed his judgment: "while the macro code is interpreted, but execution is execution, and machine code is no different. "He wrote a few articles, and proved that the virus code is compiled into binary plain text formatting possibilities. In other words, an exploit program is entirely of letters and numbers can be looked like. This roughly by changing the atomic structure of a handful of sand into gold, stunning.
Time back in 2008, the Yuan Ge suddenly found himself in ten years ago of the world may be from higher dimensions vulnerabilities bypass all mitigation measures. That is, using a script (writing) code writing attack programs, through some kind of compact design, during an attack would not trigger Microsoft DEP chip for protection.
However, the exploit code into a string of plain text that sounds simple, but very complex to implement.
Two or three months time, Yuan Ge n the following things:
Read through the detailed principles of JavaScript and VBScript, complete short Board compiled the code;
Found on the IE vulnerabilities;
Tried numerous attack paths, equipped with attack combination of vulnerability;
Complete the code writing and debugging.
This method of attack, when clean sweep from the early IE 3 to all versions of IE was introduced between 9. Even when IE 10 launched two years later, in the case of a code does not change, you can still complete the attack. Yuan Ge is most proud of the technology: DVE (data virtual execution technique), he himself called "the hand of God."
It's like having another higher-dimensional space, everyone able to see the course of action, which can only carry the result of an action.
He explained.
The code, in the eyes of Yuan Ge is just a tool. Standing on "God" person, or even a poem, a poem every word has meaning to break a system. The so-called "laughing, a forest of Scull to ashes" so-so.
However, the walking in cyberspace God touched after all business predicament. 2010 Microsoft wanted $ 350,000 to buy the "hand of God"--DVE technology, but the technology in Yuan Ge, far more than this value. The business failed, until three years later, Yuan Ge friend, head of the famous hacker TK independently submitted a counter to Microsoft technologies, won the prestigious $ 100,000. Because of the technology involved and DVE technology intersect, Microsoft only to a certain extent, plugging the DVE part of an attack.
In 2014, the Yuan Ge select DVE technical details are published on the Internet, once the land God Midgard.

"Zhan Lu Jian (zhanlu one)"
Zhanlu
Yuan Ge in anticipation of his next DVE.
To this end, the rewriting of history of Internet Security hacker guru joined Tencent, a new laboratory was established, called "zhanlu".
Tell Lei Feng Yuan Ge network (search for "Lei feng's network", public interest): "zhanlu, was cast by the spring and Autumn period master Ou Yezi sword. ' The sword of righteousness, naturalness ' is world's evaluation of zhanlu. "This is the age of the Yuan Ge some kind of State of mind. He needed a sword, a sword that can penetrate the clouds again.
Yuan Ge, while his inspiration and cannot be copied, but he realizes that need more than ever a team match.
Excavating the hole and now has reached a more advanced stage, if there is no team and a full range of technical support, something that is all by one person can't do that.
He said.
Reasons for joining Tencent, Yuan Ge gives a simple reason: "TK, Wu Shi all in, I understand them, their very identity. Security is to get people in this industry. "
March 2016 zhanlu laboratory was established. Yuan Ge stands in the cyber world of the frontier, waiting for a new ally.
The moment he becomes God, will return.